Millions Made From Exec Office365 Account Hacks: FBI Investigation
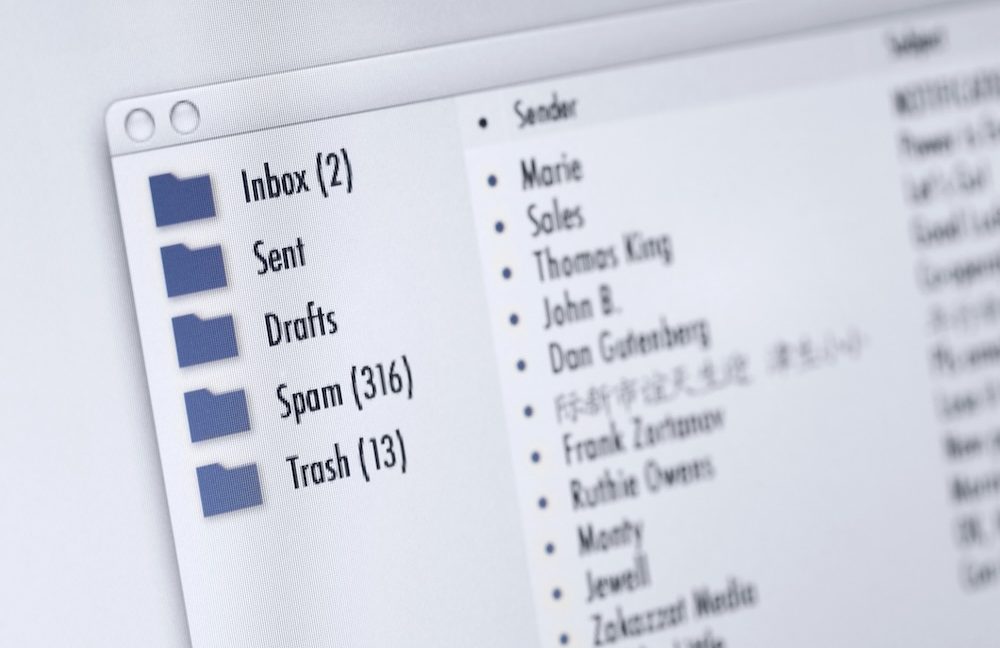
Table of Contents
The Tactics Behind Executive Office365 Account Compromises
H3: Spear Phishing and CEO Fraud:
Spear phishing and CEO fraud are the most common entry points for these attacks. Attackers meticulously research their targets, gathering information about executives' roles, communication styles, and even personal details. This allows them to craft incredibly convincing phishing emails that appear to come from trusted sources.
- Characteristics of these emails: They often contain urgent requests, mimicking legitimate business transactions or emergencies. They may include seemingly authentic attachments or links leading to malicious websites.
- Psychological manipulation: Attackers leverage urgency, fear, and authority to pressure executives into taking immediate action, bypassing their usual caution.
- Successful attack examples: Numerous cases involve attackers impersonating CEOs, CFOs, or other high-ranking officials to request urgent wire transfers or sensitive information.
Keywords: Spear phishing, CEO fraud, phishing emails, executive targeting, social engineering
H3: Credential Stuffing and Brute-Force Attacks:
Automated attacks like credential stuffing and brute-force attacks are also a significant threat. These attacks use lists of stolen usernames and passwords (obtained from previous data breaches) to try and access accounts. Brute-force attacks involve systematically trying different password combinations until a match is found.
- Leaked credentials and password databases: The dark web is a treasure trove of stolen credentials, making it easy for attackers to acquire lists of usernames and passwords.
- Importance of strong and unique passwords: Using strong, unique passwords for each account significantly reduces the risk of successful credential stuffing attacks.
- Multi-factor authentication (MFA): MFA adds an extra layer of security, requiring a second form of authentication (like a code from your phone) in addition to your password. This makes it significantly harder for attackers to gain access, even if they have your password.
Keywords: Credential stuffing, brute-force attacks, password security, MFA, multi-factor authentication
H3: Exploiting Vulnerabilities in Third-Party Apps:
Many businesses integrate third-party applications with their Office365 environment. However, poorly secured or outdated third-party apps can create vulnerabilities that attackers can exploit.
- Risks of unvetted apps: Using unvetted or insecure third-party applications dramatically increases the risk of a security breach.
- Exploiting app vulnerabilities: Attackers can exploit vulnerabilities in these apps to gain unauthorized access to Office365 accounts and data.
- Importance of app vetting and updates: Regularly update all software, including third-party apps, and carefully vet any new applications before integrating them with your Office365 environment.
Keywords: Third-party apps, application security, software vulnerabilities, Office365 security
The Financial Ramifications of Successful Office365 Executive Account Hacks
H3: Wire Fraud and Financial Losses:
Once attackers gain access to an executive's Office365 account, they can initiate wire transfers, often to overseas accounts, resulting in significant financial losses.
- Examples of financial losses: Businesses have reported losing millions of dollars due to these attacks.
- Reputational damage: Beyond the financial losses, successful attacks cause significant reputational damage, impacting investor confidence and business partnerships.
Keywords: Wire fraud, financial losses, reputational damage, business impact
H3: Data Breaches and Intellectual Property Theft:
Compromised accounts provide access to sensitive company data, including intellectual property, customer information, and strategic plans.
- Legal and regulatory implications: Data breaches can trigger costly legal and regulatory investigations and penalties.
- Data recovery and incident response: The cost of data recovery, forensic investigation, and incident response can run into hundreds of thousands of dollars.
Keywords: Data breaches, intellectual property theft, data recovery, regulatory compliance
The FBI Investigation and its Implications
H3: Scope and Objectives of the Investigation:
The FBI's investigation aims to identify and prosecute individuals and organizations responsible for these attacks. This involves tracing the flow of funds, identifying the methods used, and disrupting the criminal networks involved.
Keywords: FBI investigation, cybercrime, law enforcement, indictments
H3: Recommendations for Preventing Future Attacks:
Preventing Office365 executive account hacks requires a multi-layered approach:
- Robust security measures: Implement MFA, strong password policies, and regular security audits.
- Employee training: Educate employees about phishing techniques and social engineering tactics.
- Advanced threat protection: Invest in advanced threat protection solutions to detect and block malicious activity.
Keywords: Security best practices, cybersecurity, threat protection, security awareness training
Conclusion: Protecting Your Business from Office365 Executive Account Hacks
The sophistication and financial impact of Office365 executive account hacks cannot be overstated. Proactive security measures are crucial for protecting your business from these devastating attacks. By implementing robust security protocols, investing in advanced threat protection, and educating your employees, you can significantly reduce your risk. Don't wait until it's too late – take action today to safeguard your business from these increasingly prevalent threats. For more information on advanced threat protection solutions, [link to relevant resources/services].
Featured Posts
-
 Los Angeles Wildfires A Reflection Of Our Times Through The Lens Of Gambling Markets
Apr 29, 2025
Los Angeles Wildfires A Reflection Of Our Times Through The Lens Of Gambling Markets
Apr 29, 2025 -
 Secure Your Capital Summertime Ball 2025 Tickets The Complete Buyers Guide
Apr 29, 2025
Secure Your Capital Summertime Ball 2025 Tickets The Complete Buyers Guide
Apr 29, 2025 -
 February 20 2025 Ideas For A Happy Day
Apr 29, 2025
February 20 2025 Ideas For A Happy Day
Apr 29, 2025 -
 Fatal Shooting Of Georgia Deputy During Traffic Stop
Apr 29, 2025
Fatal Shooting Of Georgia Deputy During Traffic Stop
Apr 29, 2025 -
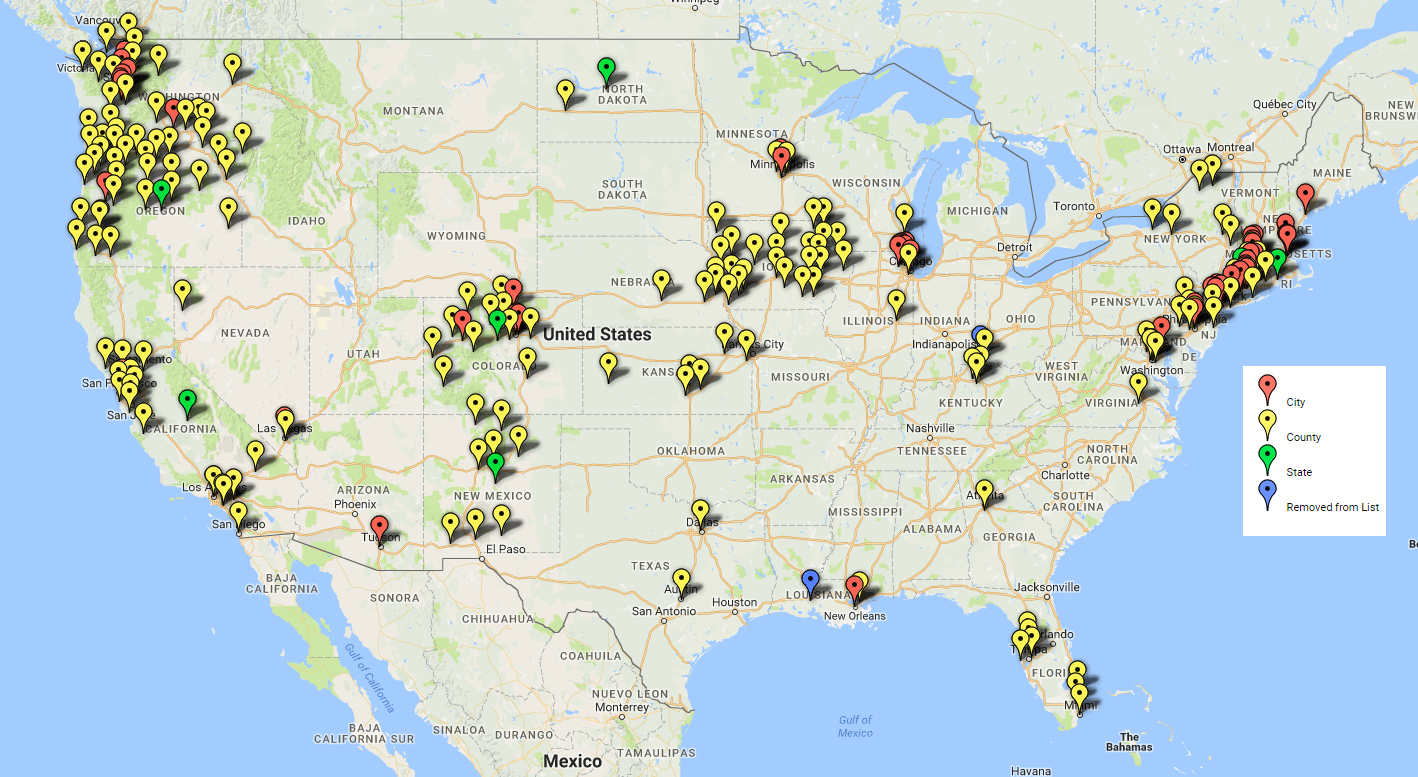 Exclusive Trumps Plan To Identify All Sanctuary Cities And States
Apr 29, 2025
Exclusive Trumps Plan To Identify All Sanctuary Cities And States
Apr 29, 2025
